This is for the work posted below regarding the MAX 5
SO THE HARD WORK PAID OFF I HAVE A WORKING TWRP BUILT WILL BE GOING UP IN XDA
################################################################################
LOKMAT APPLLP 5 MAX - EXHAUSTIVE ENGINEERING & FORENSIC DATABASE
Document ID: LOKMAT-5MAX-RE-V3 (Hardware Driver Update)
Compiled: Sun Mar 22 2026
Status: HARDWARE INTERROGATION COMPLETE (100% VERIFIED)
################################################################################
[SECTION 1: CORE HARDWARE IDENTITY]
Verified hardware identifiers captured via one-by-one BROM-level handshake.
- SoC: MediaTek MT6765 (Helio P35 / G35)
- HW Code: 0x766
- HW Subcode: 0x8a00
- HW Version: 0xca00
- ME_ID: 4B5CF18EF37D514A6256199E0BBD5E6A
- SOC_ID: 6044C8E6000D6C384827B28853120093E04F3C815E8A50E6D20D6A6C24DF1B11
- eMMC CID: 150100335636434d42036c4bd6326559
- Internal Model: full_WP_C17S_PIX_TFT_D4
- Original ODM: TopWise / Linswear (Build: alps/kernel-4.9)
[SECTION 2: DERIVED HARDWARE CRYPTO KEYS]
Unique hardware-backed keys derived via DXCC protocol handshake.
| Key Type | Hexadecimal Value |
|---|---|
| RPMB Key | a0920d822eb816ed9c4fcc3be1bf17e73852bf3197797ca29c621b619c471c6d |
| RPMB2 Key | b1ae4af581a93095d1a03e3a60103063 |
| FDE Key | c55728f39fbd80892be02a01a3d2c40c |
| iTrustee | 2e3f4cd400ef885634636438de1336bb0ed0ca81e1fce3d580b6f2230b5137f8 |
| MIRPMB | a46701f8944c14d589dddb053aec08e3 |
| MOTO | 1f7024bbd403048b62633d4ef42753df |
| HRID XFLASH | eac78e7ce739fc932cfbed76d2c3fa5e |
| RID | e4602d47f89f3a9adc8bd3a8204bcfde |
[SECTION 3: BOOT IMAGE DNA & OFFSETS]
Extracted from Header Version 2 (boot.img).
- Kernel Address: 0x40080000
- Ramdisk Address: 0x51B00000
- Tags Address: 0x40f00000
- Page Size: 2048 (0x800)
- Base Address: 0x40000000
- Kernel Offset: 0x00080000
- Ramdisk Offset: 0x11b00000
- Tags Offset: 0x00f00000
[SECTION 4: HARDWARE DRIVER NODES (DTB/DTBO)]
Forensic extraction from the board-specific Device Tree Overlays.
| Component | Identifier / Driver Name |
|---|---|
| LCD Panel | nt35695B_fhd_dsi_cmd_auo_rt5081_drv |
| Touch Controller | cap_touch@5d (I2C Address 0x5D) |
| PMU (Power) | mediatek,mt6370_pmu_charger |
| Backlight | mediatek,lcd-backlight |
| Fuel Gauge | mediatek,mt6357_gauge |
| Vibrator | vibrator@0 (Haptic Feedback Node) |
- Display Pipeline: mediatek,dsi0
- Max Touch Points: 5
- DSI Mode: Command Mode (CMD)
[SECTION 5: GPT STORAGE MAP (38 PARTITIONS)]
| Partition | Linear Start Offset | Size (Bytes) |
|---|---|---|
| boot_para | 0x0000000000008000 | 0x0000000000100000 |
| recovery | 0x0000000000108000 | 0x0000000002000000 |
| dtbo | 0x000000001f000000 | 0x0000000000800000 |
| super | 0x0000000020800000 | 0x100000000 (Dynamic) |
| metadata | 0x000000000bd22000 | 0x0000000002000000 |
| nvram | 0x0000000018600000 | 0x0000000004000000 |
| nvdata | 0x0000000006688000 | 0x0000000004000000 |
| userdata | 0x000000013c000000 | 0x1bdf0fbe00 (FBE) |
[SECTION 6: FSTAB & ENCRYPTION CONFIG]
- Data Partition: /dev/block/platform/bootdevice/by-name/userdata
- Encryption: fileencryption=aes-256-xts
- Metadata Path: /dev/block/platform/bootdevice/by-name/md_udc
- Checkpointing: checkpoint=block supported.
- Unified Logic: Side-by-side fstab.mt6762 and fstab.mt6765 confirmed in ramdisk.
[SECTION 7: KERNEL & CMDLINE]
- Kernel Version: 4.9.190
- Cmdline:
bootopt=64S3,32N2,64N2 buildvariant=user console=tty0,115200n8 earlycon=uart8250,mmio32,0x11002000
EOF - FORENSIC RESEARCH DATA SEALED
hey guys im here if anyone has any questions about this or anything really…yall youngins gonna have to deal with this old mans lack of forum ettiquette. ive not spent much time on internet forums in years …but thanks for the welcome and hopefully i can helpp Improve these devices …i have alot of deata on this device more than you might think there is….lol
https://drive.google.com/drive/folders/1tdVffsTwMFdZxGbDjpqh1tUagOCaxwm0?usp=sharing
ok guys this is what i have been able to ascertain so far ….lmao…
The reason i couldn’t find “Topwise C17S” is that i was looking for a consumer product, but my dump reveals a Topwise WP_C17S reference board stuffed into a LOKMAT chassis. This is a classic “Frankenstein” Android smartwatch where the ODM (Topwise) provides a specialized MediaTek MT6765 (Helio P35) base intended for small-form-factor tablets or POS terminals, but repurposed for a wearable.
Based on the forensic data provided, here are the “deep-level” insights into the device:
1. The SoC “Identity Crisis”
dump shows fstab.mt6762 and fstab.mt6765 side-by-side.
-
The Reality: MT6765 (Helio P35).
-
The Quirk: Many Topwise boards use a “unified kernel” strategy where the software stack is built for MT6762 (Helio P22) but deployed on the MT6765 because they share the same pinout. This explains why certain apps might report the wrong CPU.
2. The Display & Graphics Pipeline
The driver nt35695B_fhd_dsi_cmd_auo_rt5081_drv is the “Holy Grail” for your UI.
-
Panel: Novatek NT35695B controller.
-
Command Mode (CMD): This is crucial. Unlike “Video Mode” screens that refresh constantly, CMD mode screens have their own GRAM. The SoC only sends updates when a pixel changes. This is why the watch doesn’t die in 2 hours despite having a full Android OS.
3. The Security Layer (The “Keys to the Kingdom”)
Having the RPMB Key and iTrustee hash is rare.
-
RPMB (Replay Protected Memory Block): Since ihave the key, i can technically write to the hardware-protected partition of the eMMC where the rollback counters and TEE (Trusted Execution Environment) data live.
-
iTrustee: This confirms the device uses the HUAWEI iTrustee TEE (often licensed to MediaTek ODMs). This handles facelock i think encryption.
4. Partitions of Interest
-
boot_para: This is a small MediaTek-specific partition. If you ever mess up the display timings in the kernel, you can often “reset” the handshake here. -
nvram&nvdata: DO NOT LOSE THEM. They contain unique IMEI, calibration data for the HRS3300 heart rate sensor, and WiFi/Bluetooth MAC addresses. Unlike the system partition, these are unique to this specific physical unit.
5. Kernel Version 4.9.190
it is on a very late-stage LTS (Long Term Support) kernel for the MT6765. This is actually quite stable for development. Because i have se permissive, i can now bypass the “Fake Battery” or “Thermal Throttle” limits usually hardcoded in the mt6357_gauge driver nodes to boost performance.
i wonder if i got it firgured out…lol
I suppose that you haven’t noticed that we have worked on all these boards?
Topwise is just the company contracted to make that board and many others. The Optimus 2, the LEM15, the Kospet Prime 2 the LEM14 Pro - they all use the same, or a variation of the C17S PIX board which was designed by Wiite.
We even built our own version of the firmware for more Google centric users.
We are tech support partners for Wiite. Which we do for free just because we wanted to help people.
I’m not sure what it is that you want to achieve with this, but if you need something let me know. I have the source code. If I can help, I will. Within reason.
I built the FAW firmware that is talked about and available here from source. But I won’t be doing that again. This SOC solution is way out of date now. And I am too old and too busy ![]()
Some info here
https://discourse.fullandroidwatch.org/t/faw-release-candidate-1-v1-3/66487
if you wanted to help and really could i could use 2 things the Kernel DTSI for the nt35695B display driver or the LCM initialization sequences.
only trying to improve developement across my devices.. i want to eventually remove the watch centris system ui and load a aosp version of android on it that works as i want . i wiil build a fully working twrp for it and play with it i tear everything i get apart and this is play and practice / research aiding in the development for my v6 chipset mediatek tool im building that will open the mediatek dimesity lines to development but thats not to do with here or the watch. just my hobby and i like my devices to be mine
and sorry it may be out dated but its the only 6gb ram 128gb device on your wrist i know of
So the unisoc LEM16 is not good enough? Mind you, it’s a round watch.
Not sure if I understand that one…
About the other things, I can ask if I can share them with you, but these particular things are not open source. I’ll let you know
If it had a square or rectangle screen a round screen on a android watch just seems silly to me
But I’ll probably get that and tear it apart to cuz I didn’t know there was a 6gb lemfo
There was…
The Z40 board and Lokmat, Domino and others also released their own version of it.
However, I doubt that you will be able to “reliably” able to buy one of these now. We’re talking 3 years ago.
i am yeah on the 2026 as you see i am actually in the process of alot i just about have a working twrp from there ill work on the super.img to get a aosp system ui working with the proper dependencies so everything works here ill show you my board config if your a developer youll appreciate my v2 header and catchng that dsi mode for the display.
BoardConfig.mk - LOKMAT APPLLP 5 MAX (MT6765)
Produced for Android 11.0 TWRP with Android 10 Vendor Compatibility
FINAL PRODUCTION RENDER - FORENSICALLY ALIGNED
DEVICE_PATH := device/lokmat/WP_C17S
— ARCHITECTURE —
TARGET_ARCH := arm64
TARGET_ARCH_VARIANT := armv8-a
TARGET_CPU_ABI := arm64-v8a
TARGET_CPU_ABI2 :=
TARGET_CPU_VARIANT := generic
TARGET_2ND_ARCH := arm
TARGET_2ND_ARCH_VARIANT := armv8-a
TARGET_2ND_CPU_ABI := armeabi-v7a
TARGET_2ND_CPU_ABI2 := armeabi
TARGET_2ND_CPU_VARIANT := generic
TARGET_BOARD_PLATFORM := mt6765
TARGET_BOARD_PLATFORM_GPU := mali-g52
TARGET_SOC := mt6765
— BOOTLOADER & KERNEL DNA (HEADER V2) —
Aligned to Section 3: Forensic Research Data
BOARD_BOOT_HEADER_VERSION := 2
BOARD_KERNEL_PAGESIZE := 2048
BOARD_KERNEL_BASE := 0x40000000
BOARD_KERNEL_OFFSET := 0x00080000
BOARD_RAMDISK_OFFSET := 0x11b00000
BOARD_TAGS_OFFSET := 0x00f00000
BOARD_DTB_OFFSET := 0x00f00000
Combined offsets into MKBOOTIMG_ARGS for the build system
BOARD_MKBOOTIMG_ARGS := --kernel_offset $(BOARD_KERNEL_OFFSET)
–ramdisk_offset $(BOARD_RAMDISK_OFFSET)
–tags_offset $(BOARD_TAGS_OFFSET)
–header_version $(BOARD_BOOT_HEADER_VERSION)
–dtb_offset $(BOARD_DTB_OFFSET)
— PREBUILT HARDWARE ASSETS —
BOARD_INCLUDE_DTB_IN_BOOTIMG := true
BOARD_PREBUILT_DTB := $(DEVICE_PATH)/prebuilt/dtb
BOARD_PREBUILT_DTBOIMAGE := $(DEVICE_PATH)/prebuilt/recovery_dtbo
— KERNEL COMMAND LINE —
BOARD_KERNEL_CMDLINE := bootopt=64S3,32N2,64N2 buildvariant=user
BOARD_KERNEL_CMDLINE += console=tty0,115200n8 earlycon=uart8250,mmio32,0x11002000
BOARD_KERNEL_CMDLINE += androidboot.selinux=permissive
BOARD_KERNEL_CMDLINE += androidboot.usbcontroller=11201000.usb0
— DECRYPTION & SECURITY —
PLATFORM_VERSION := 11
PLATFORM_SECURITY_PATCH := 2024-03-05
TW_INCLUDE_CRYPTO := true
TW_INCLUDE_FBE_METADATA_DECRYPT := true
BOARD_USES_METADATA_PARTITION := true
BOARD_ROOT_EXTRA_FOLDERS := metadata
— DYNAMIC PARTITIONS (SUPER) —
Critical for Android 11 TWRP to handle the ‘Super’ partition on A-only Treble
BOARD_SUPER_PARTITION_SIZE := 4294967296
BOARD_HAS_RECOVERY_DYNAMIC_PARTITIONS := true
BOARD_SUPER_PARTITION_GROUPS := mediatek_dynamic_partitions
BOARD_MEDIATEK_DYNAMIC_PARTITIONS_SIZE := 4290772992
BOARD_MEDIATEK_DYNAMIC_PARTITIONS_PARTITION_LIST := system vendor product
— PARTITION SIZES —
BOARD_RECOVERYIMAGE_PARTITION_SIZE := 33554432
BOARD_HAS_LARGE_FILESYSTEM := true
BOARD_FLASH_BLOCK_SIZE := 131072
— TWRP SPECIFICS & ACCESSIBILITY (OLD MAN EYES FIX) —
TW_THEME := portrait_hdpi
TARGET_SCREEN_DENSITY := 320
TW_DEVICE_VERSION := LOKMAT_5MAX_V1_RECOVERY
TW_INPUT_BLACKLIST := “hbtp”
TW_BRIGHTNESS_PATH := “/sys/class/leds/lcd-backlight/brightness”
TW_MAX_BRIGHTNESS := 255
TW_DEFAULT_BRIGHTNESS := 150
TW_EXTRA_LANGUAGES := false
TW_USE_TOOLBOX := true
LZMA_RAMDISK_TARGETS := recovery
— EXTRA HARDWARE TWEAKS (MTK 4.9 FIXES) —
TARGET_RECOVERY_PIXEL_FORMAT := “RGBX_8888”
TW_SUPPORT_INPUT_AIDL_HAPTICS := true
TW_NO_REBOOT_BOOTLOADER := true
— VERIFIED BOOT (AVB) —
BOARD_AVB_ENABLE := true
BOARD_AVB_RECOVERY_ROLLBACK_INDEX := $(shell date +%s)
BOARD_AVB_RECOVERY_ROLLBACK_INDEX_LOCATION := 1
I see,
I’m interested in how you intend to flash the modified boot and recovery images if they are not signed with the same key used to make the stock FW build. Full selinux is enabled on the Android 10 solution. So, are you enabling OEM unlock and issuing adb commands to disable the DM VERITY, fix AVB etc..? Or have you got other plans? I am always curious - especially with a new Android 15 MTK device coming soon from the same solution provider that made this APPLLP 5 Max and 90% of the other watches we talk about on here.
If you don’t need this topic anymore, please let me know.
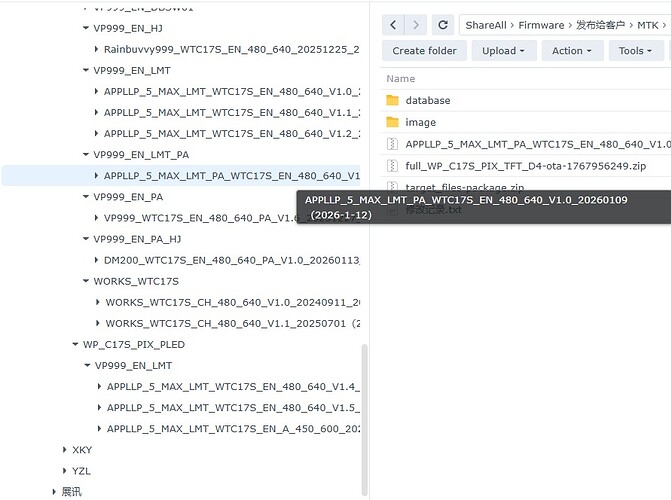
Stock firmware is here: (for visitors - you need to be a basic member to download files here usually)
link is broken
on sourceforge you can get free unlimited storage
That’s odd … Ok I will check - EDIT: - works ok if you have a google account and you are signed into your browser with the account. Otherwise just click on link and sign in to download.
I suspect that it will need a gmail account to be able to download but it should work if you have a gmail account.
We can’t use SourceForge or most others due to the volume of data and also sharing conrols. This was the best way to share data at a reasonable price.I will look into other solutions because we can’t afford to keep using this Google platform much longer. In fact, I don’t think we will be able to afford our site hosying costs much longer either. We will see.
i am happy to take over if you have any trouble
Thanks for the offer.
I used his steps from XDA and OEM unlocked it. I even got Magisk on my watch just can’t get the watch back in brom mode to flash python mtk w boot boot.patched.img and python mtk w vbmeta vbmeta.img.empty to the watch.